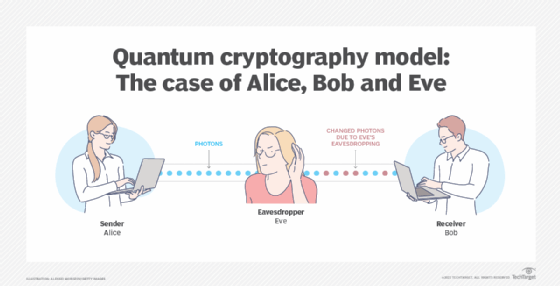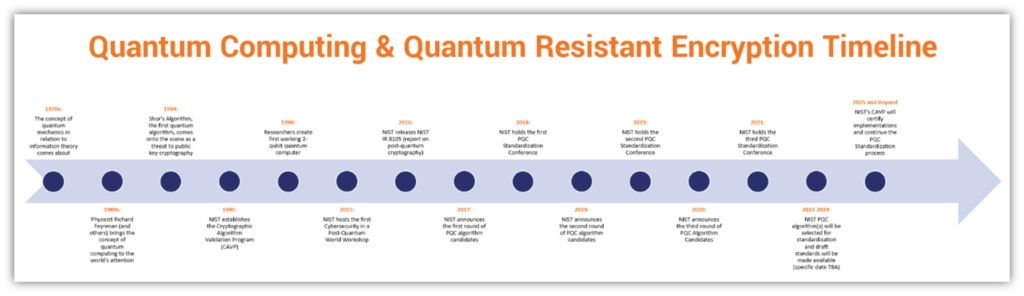
A Look at Quantum Resistant Encryption & Why It's Critical to Future Cybersecurity - Hashed Out by The SSL Store™

Quantum computing will break today's encryption standards - here's what to do about it | About Verizon
Post-Quantum Cryptography: A Look At How To Withstand Quantum Computer Cyber Attacks - CB Insights Research